When the Node Shifts
On the topology of strategy and the systems behind stability
We normally reserve new posts for once a week, but a piece published this morning by our colleague and longtime collaborator Dr. Isaiah Wilson III was too directly connected to what we have been building here to let sit until next week.
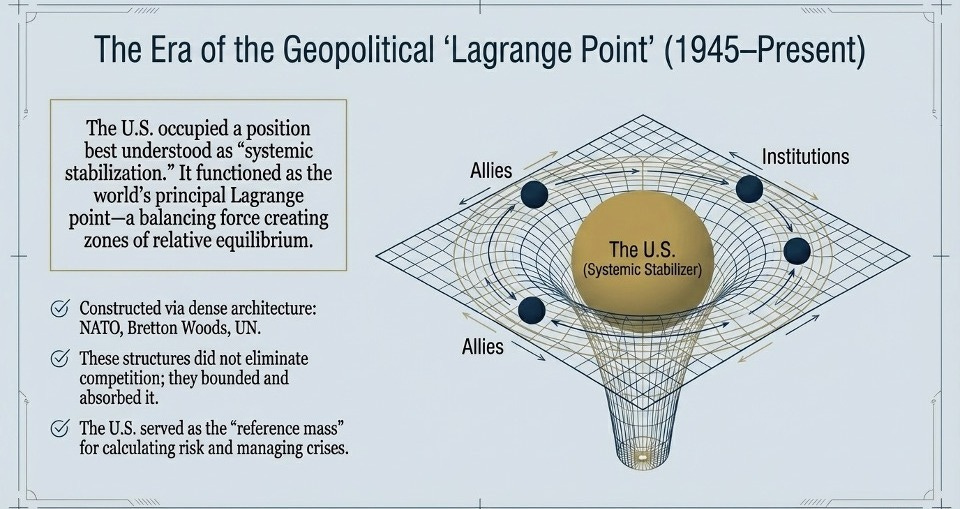
Dr. Wilson, writing on his Compound Security, Unlocked Substack, lays out a framework for thinking about strategic stability in what he calls a three-body world: external competition, internal cohesion, and institutional legitimacy interacting in ways that are inherently nonlinear and resistant to control. His central argument is that the goal of strategy is no longer dominance but coherence, and that when a system loses its Lagrange point, the stabilizing function it provided doesn’t simply go vacant. It gets contested, hedged around, and partially substituted in ways that are hard to see until something breaks.
We found ourselves reading it through the lens of the work we’ve been doing on ecosystem mapping, because the structural challenge Ike is describing is remarkably similar to the one we encounter at much smaller scales. Consider a concrete example: when an ally shifts position on a significant issue, you are not facing a diplomatic problem in isolation. You are facing a topology problem. The question is where that actor sits in the broader network of relationships, what functions it has been performing, and what options exist for keeping the system in equilibrium. That is exactly the kind of question that a role-network map is designed to answer.
The Same Problem, Smaller Scale
In the Capital Follows post from yesterday, we wrote about the difference between counting actors and mapping functions. In any ecosystem, the meaningful unit of analysis is not the organization but the role it plays: who is actually providing capital, who is genuinely developing talent, who is connecting actors who would not otherwise find each other. When you map by function rather than by actor, structural patterns emerge that standard metrics never surface. You can see where a function is being performed by only one actor, which makes it a single point of failure. You can see which connections between functions are strong and which are nominal. You can see, concretely, what changes if a given node shifts.

That same logic applies to security ecosystems. Ike’s Lagrange point concept is essentially a description of a node that was performing multiple stabilizing functions simultaneously: providing predictability, absorbing tension, and sustaining institutional credibility. When that node becomes intermittent, the question is not simply how to replace it. The question is which of its functions were genuinely load-bearing, which connections have to be rebuilt or rerouted, and which actors are positioned to absorb part of the load. Those are network topology questions. They require a map.
Beyond Startup Ecosystems
This is where we think the ecosystem mapping methodology we have been developing has potential applications that go beyond startup ecosystems. The underlying problem is the same: a complex system whose structure is not visible to the people trying to manage it. The standard response is more reporting, better dashboards, richer data on outcomes. But as we keep arguing in this space, more data about the wrong things does not close the gap. It produces more confidence in a picture that still does not reflect the underlying structure.

What changes the picture is a different unit of analysis. Not outputs, but roles. Not actor counts, but connection strength. Not what the system is producing, but how the critical functions relate to each other, where they are fragile, and what a targeted intervention at a specific node would actually change.
Ike closes his piece with a phrase worth sitting with: stability must be cultivated through design, not engineered through control. That is a precise description of what good ecosystem mapping is for. You cannot manufacture resilience by adding resources to a system you cannot see. You can start to cultivate it once you have a clear picture of where the roles are performed, where the connections are weak, and what a well-placed intervention would actually shift.
We are early in thinking through how this methodology translates to the security and strategic contexts Ike is working in. But the structural logic travels. If these questions connect to work you are doing, we would like to hear from you.